Cheese CTF | THM Writeup
Introduction
Detailed walkthroughs for Cheese CTF CTF challenges on TryHackMe .
Initial Foothold
echo "10.10.16.91 cheese.thm" >> /etc/hosts
Mappped the ip to domain certain-doom.thm.
nmap
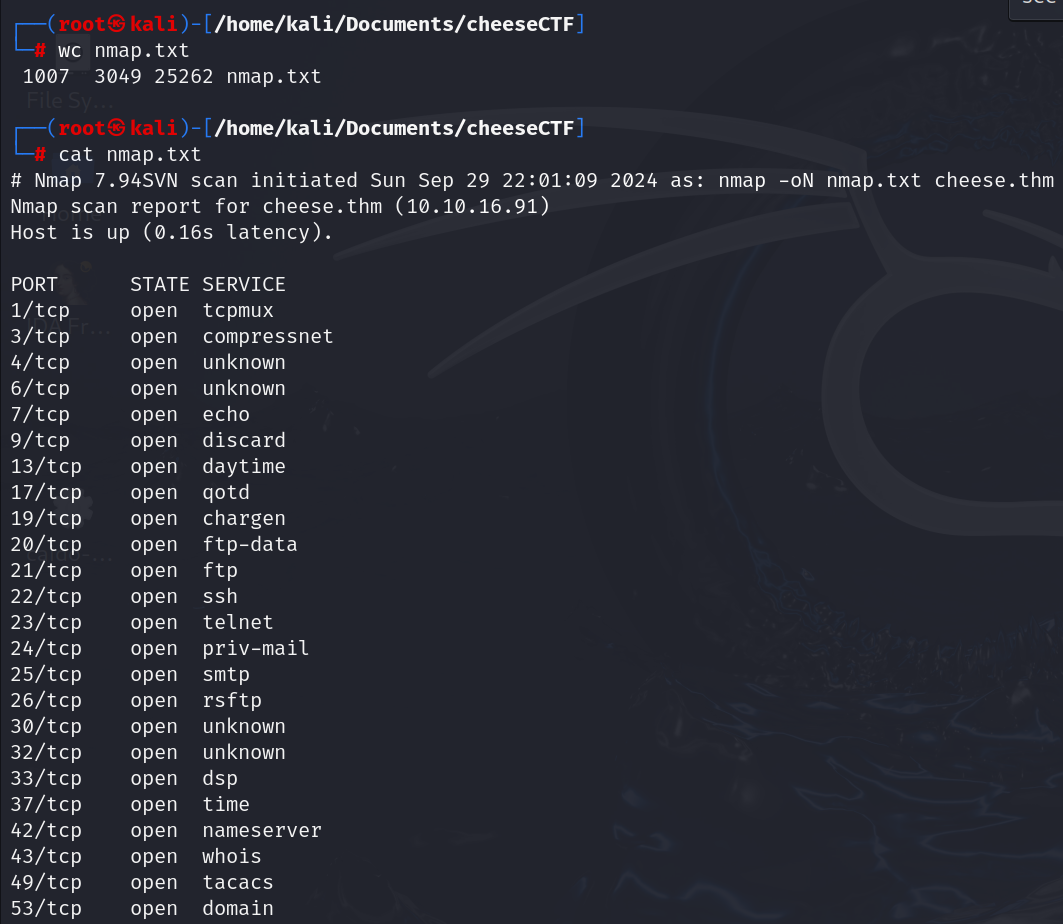
Initial scan gives result as lot (n) number of ports open. May be they are tricking us not to look for what we want.
$ nmap cheese.thm -sC -sC -p22,80
Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-09-29 22:48 IST
Nmap scan report for cheese.thm (10.10.16.91)
Host is up (0.16s latency).
PORT STATE SERVICE
22/tcp open ssh
| ssh-hostkey:
| 3072 b1:c1:22:9f:11:10:5f:64:f1:33:72:70:16:3c:80:06 (RSA)
| 256 6d:33:e3:bd:70:62:59:93:4d:ab:8b:fe:ef:e8:a7:b2 (ECDSA)
|_ 256 89:2e:17:84:ed:48:7a:ae:d9:8c:9b:a5:8e:24:04:bd (ED25519)
80/tcp open http
|_http-title: The Cheese Shop
Nmap done: 1 IP address (1 host up) scanned in 6.13 seconds
I’ve confirmed that port 22 and port 80 are open.
12 minutes to read

